Plugins
Extend DarkRide with plugins. Add new protocols and functionality.
Capture HTTPS traffic, decompile APKs, hook the runtime, drive the device — all from your browser. Every tool exposed as MCP, so your agent can drive it the way you do.
one local web app · one device session
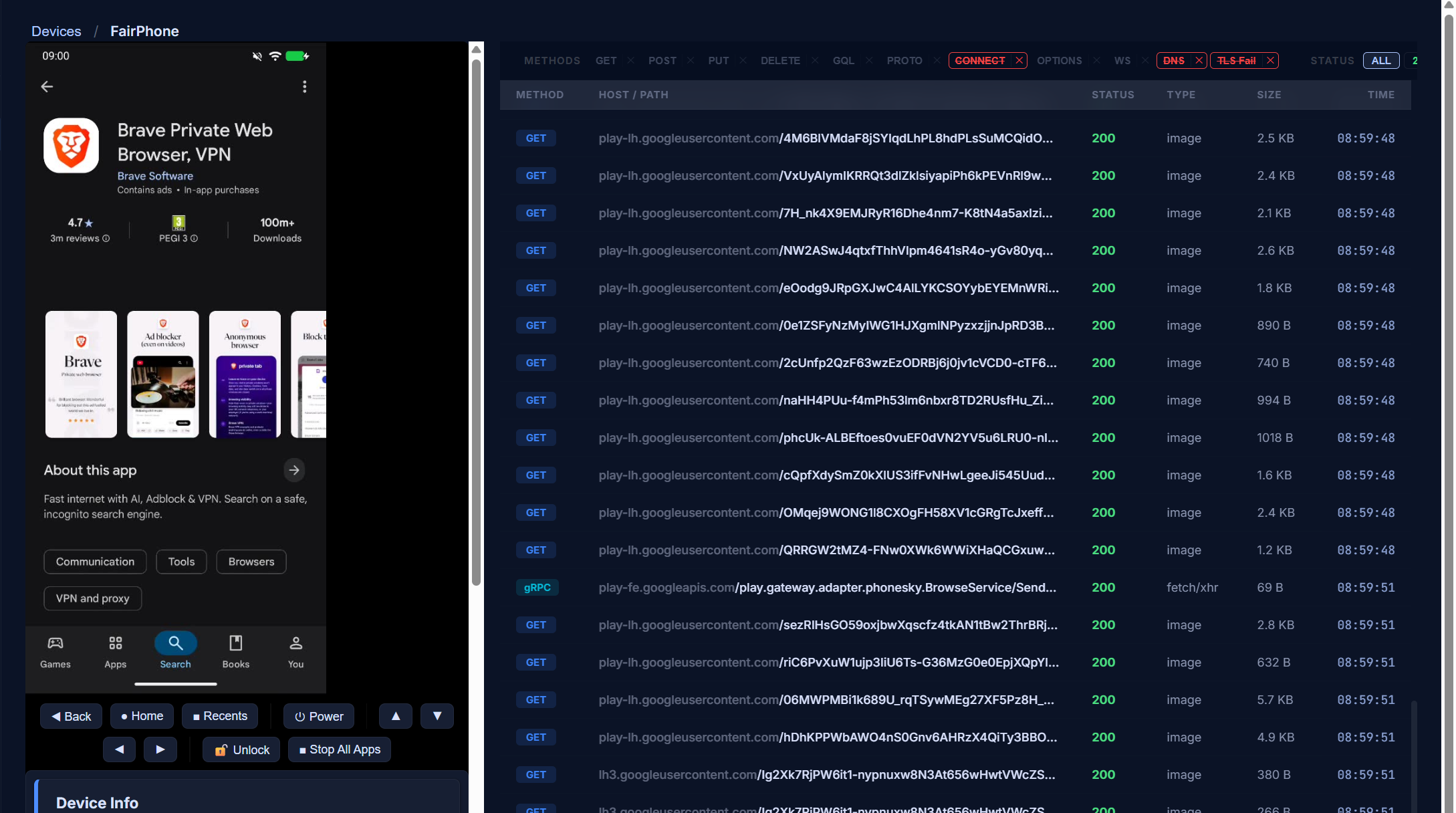
WireGuard transparent proxy. No phone-side proxy config. Filter, search, save — and hook from automation scripts.
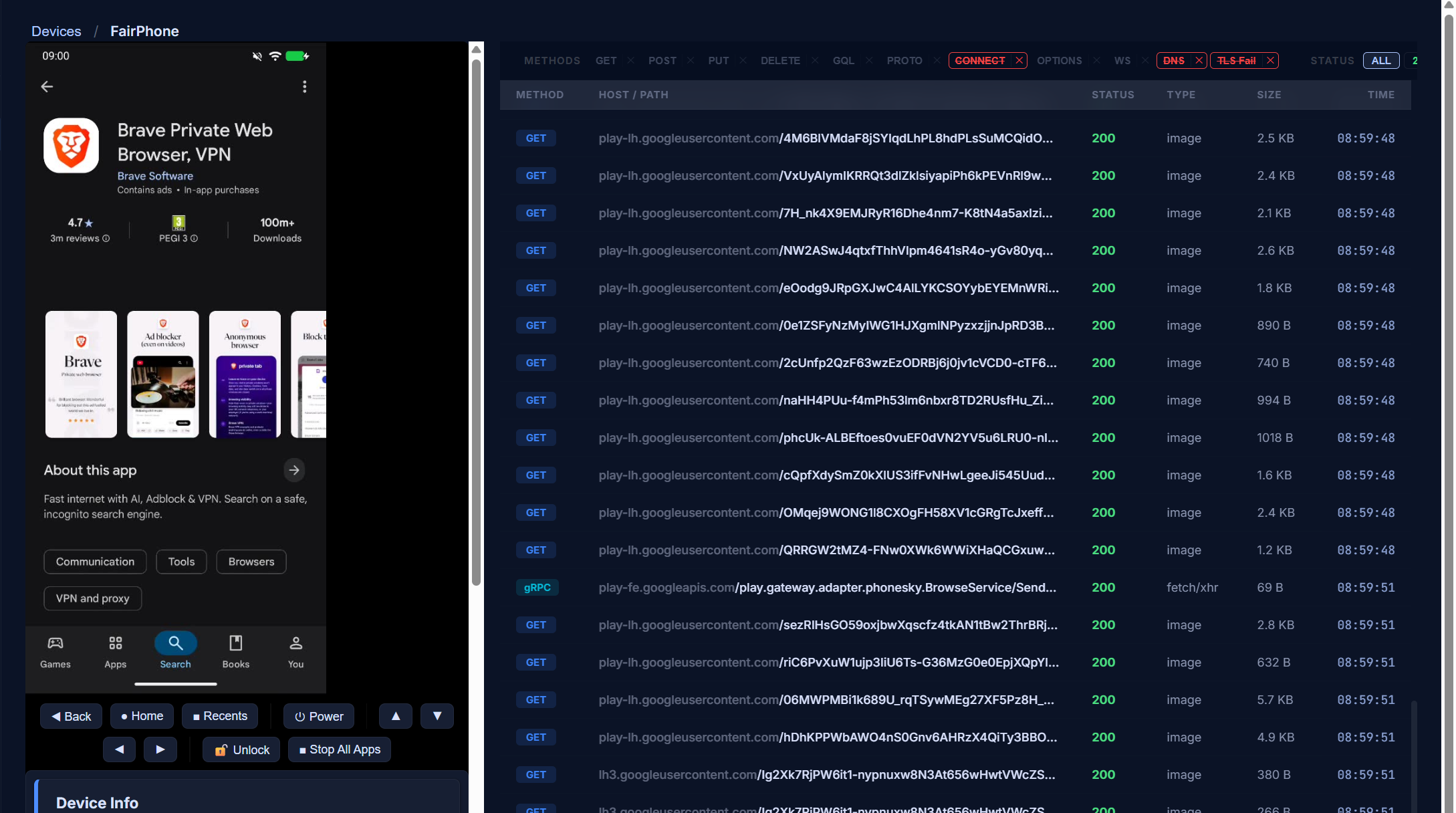
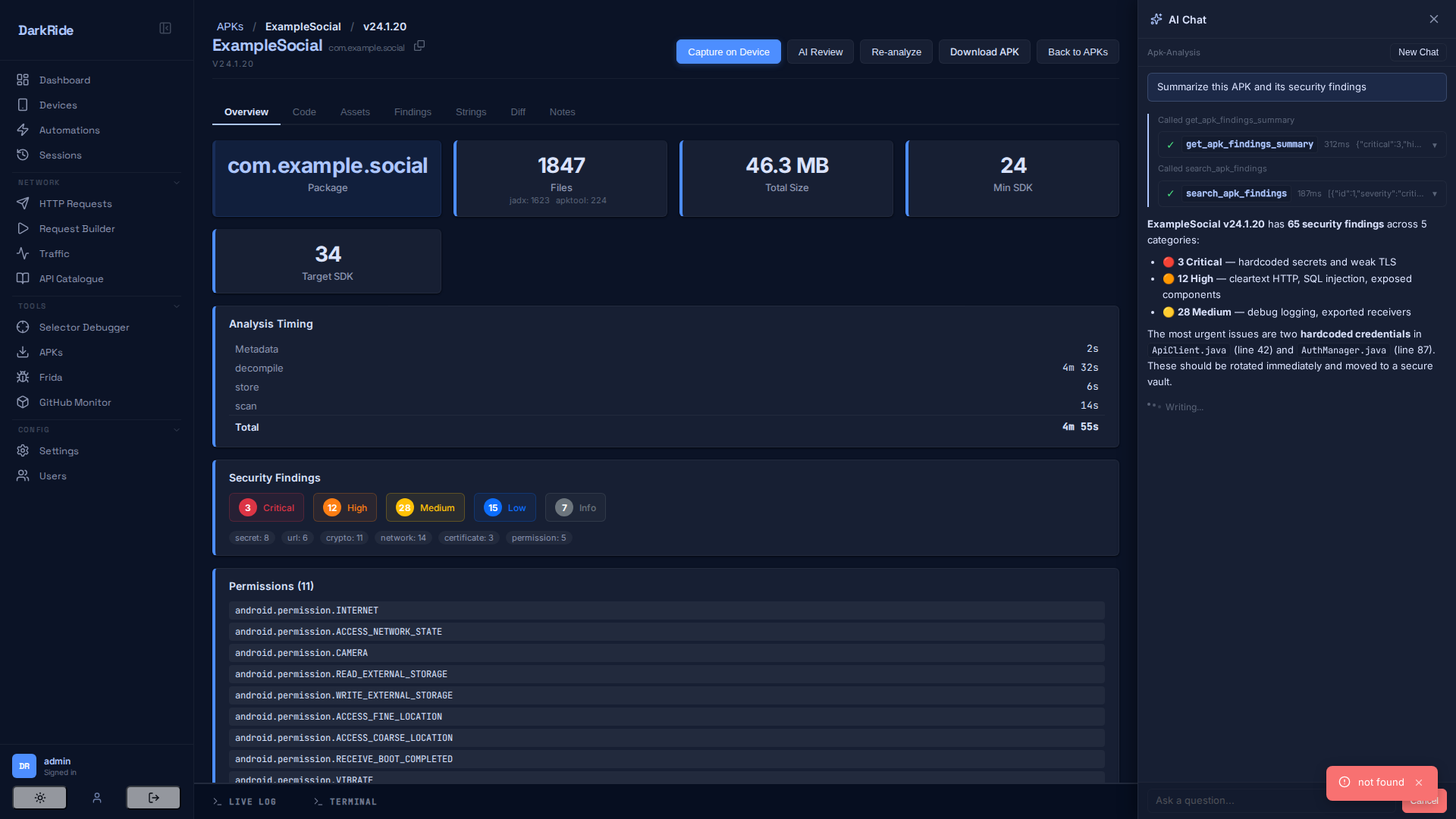
Decompile APKs, diff versions, search strings, and let the AI agent navigate the code with 40+ real tools. Native, React Native, Hermes, and Flutter supported.
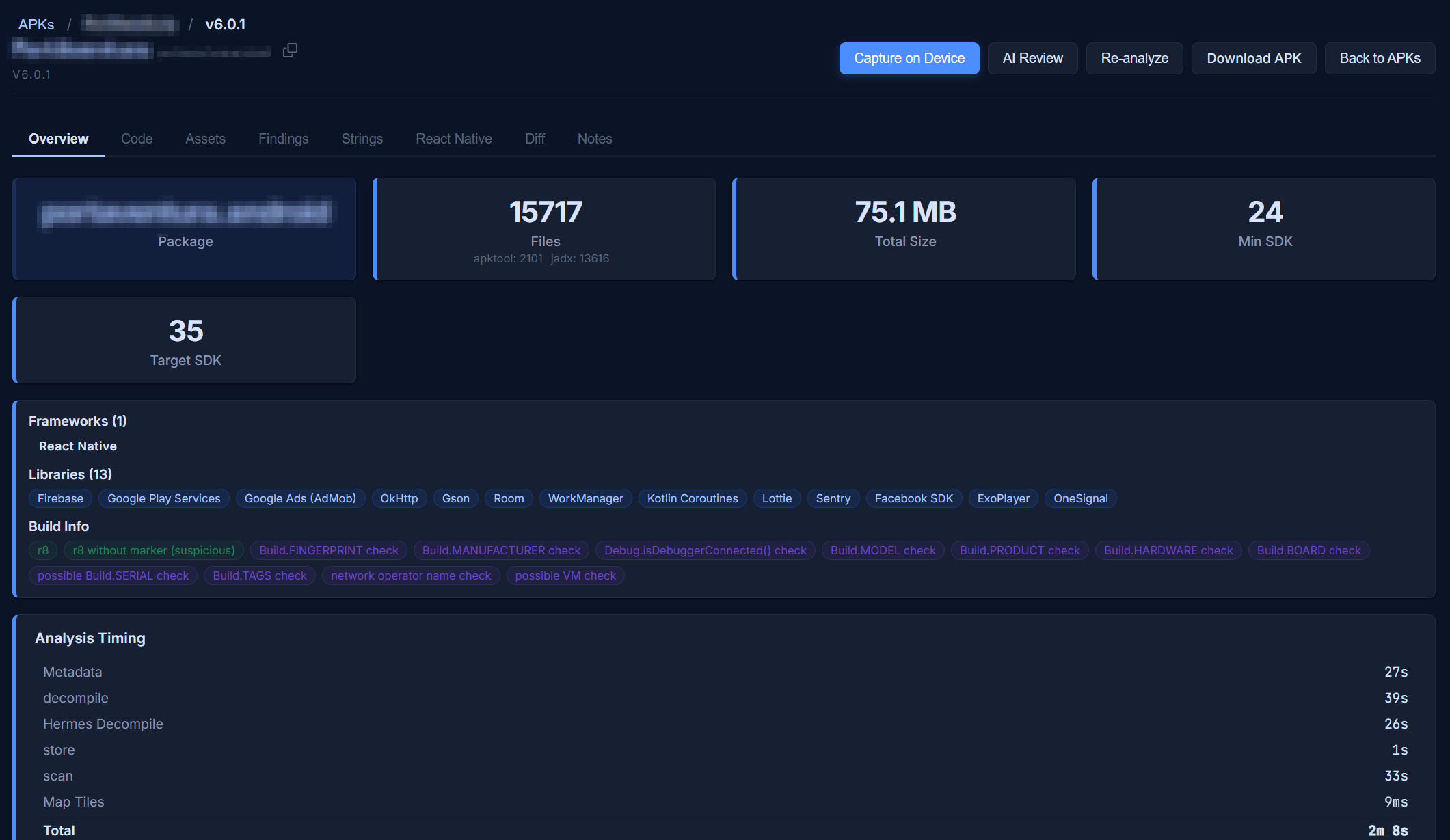
Drive real Android devices with a fully typed DeviceAPI. Monaco editor with autocomplete, session history with screenshots and traffic per run. iOS automation is on the roadmap.
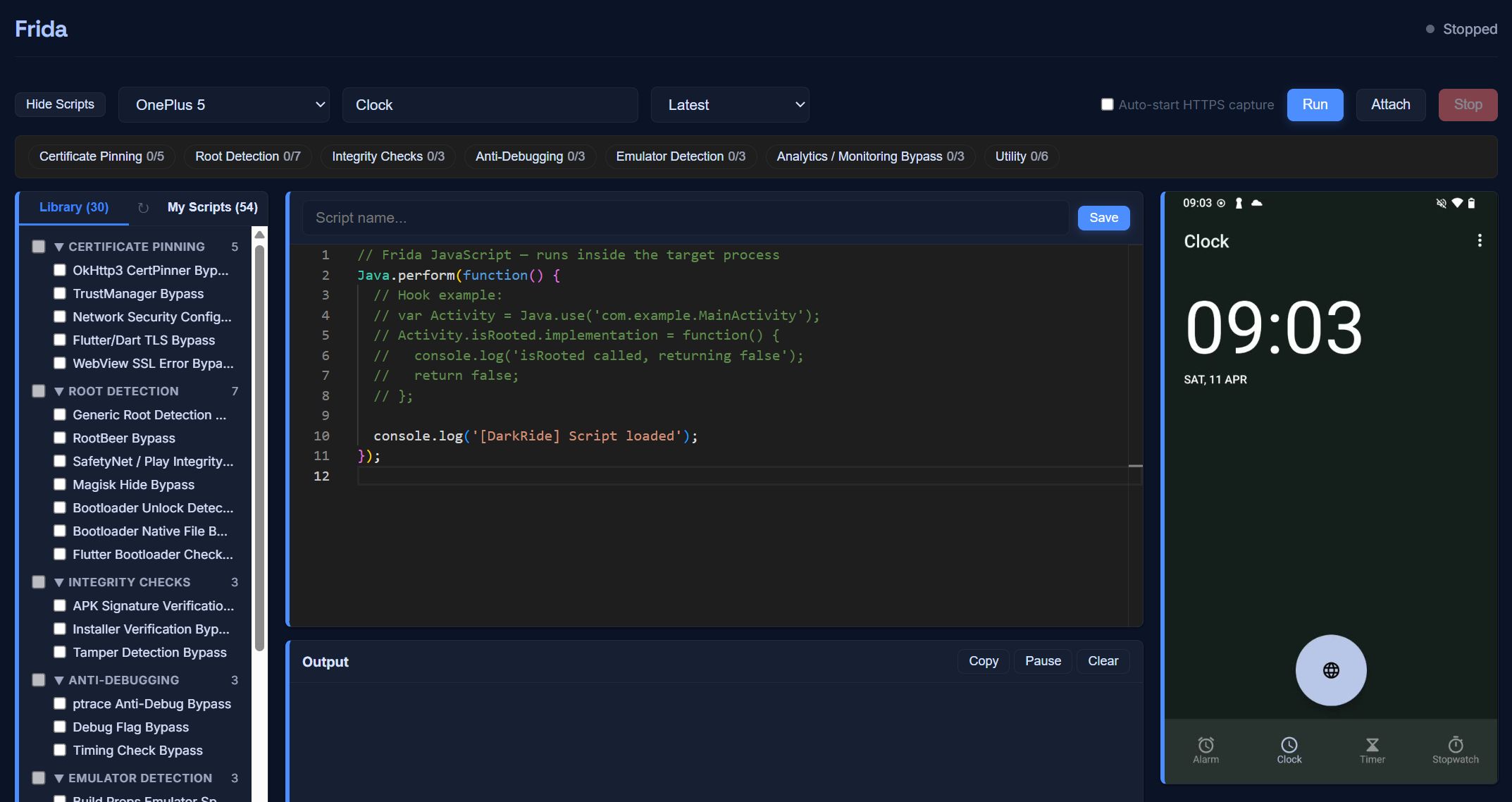
Curated script library, Monaco editor, live device mirror. SSL pinning bypass, root detection bypass, anti-debugging — pre-baked, version-pinned.
Every DarkRide capability is exposed as MCP — the protocol Claude, Cursor, and other AI clients use to call external tools. Your agent can capture traffic, decompile APKs, run Frida hooks, and drive the device — directly, in the same session, with shared state.
Extend DarkRide with plugins. Add new protocols and functionality.
Source open forever. Commercial dual-license available for closed deployments.
ThemeParks.wiki has been building reverse-engineering tools for years. Over that time, a stack of custom proxies, decompilation scripts, and analysis tools grew up around it. DarkRide is that stack — cleaned up, given a UI, and released for everyone else doing similar work.
→ It runs in production today. The repo isn’t a lab project.
Node 22+, a rooted Android device (or an emulator), and about 10 minutes.
git clone https://github.com/DarkRideApp/DarkRide.git
cd DarkRide
npm install
npm run devSee the installation guide for platform-specific setup.
DarkRide is maintained by one developer in their spare time. If it's useful to you or your team, consider sponsoring continued development.